Microsoft Remote Desktop Save Password
-->
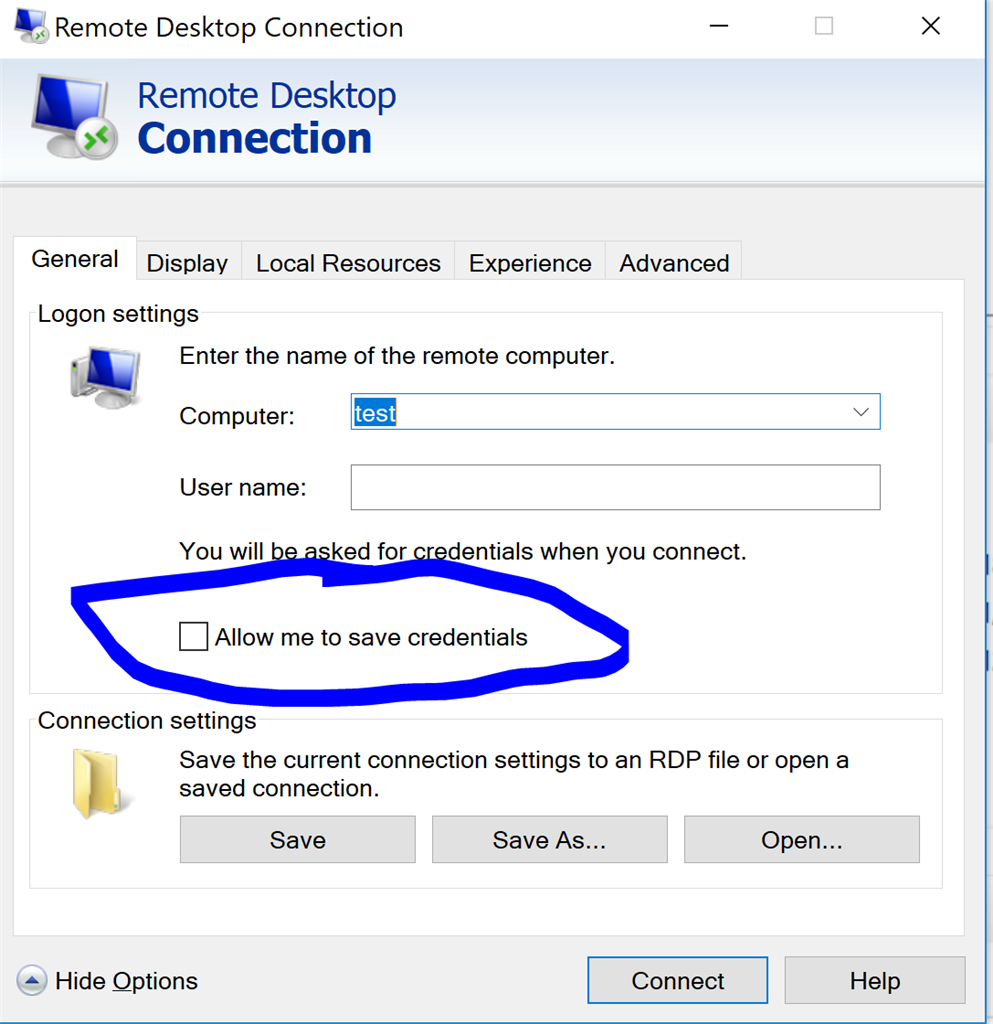
The built-in Windows Remote Desktop client (mstsc.exe) allows you to save the username and password used to connect to the remote computer.Using a saved RDP credentials, the user doesn’t need to enter the password each time to connect to the Remote Desktop. Microsoft Remote Desktop Services. Where you have to set the proper domain user and enter the password - I do not click save password (wouldn't want someone to.
Start typing “Remote Desktop” on Start Screen and click it from the search list to launch. Click Show Options to extend the option list. Type in the username, check the option “ Allow me to save credentials “, and click Save As button to save this setting in a dedicated RDP file, preferably maybe on the desktop. Cannot save remote desktop password in Windows 10 Home. When I am using the remote desktop client on Windows 10 Home to connect to a Windows 10 Pro system, I cannot save my password as I can on other systems. Is this a bug or restriction in Windows 10 Home edition? This is a new Dell XPS with Windows Signature Edition.
Applies to
- Windows 10
- Windows Server 2016
Introduced in Windows 10, version 1607, Windows Defender Remote Credential Guard helps you protect your credentials over a Remote Desktop connection by redirecting Kerberos requests back to the device that's requesting the connection. It also provides single sign-on experiences for Remote Desktop sessions.
Administrator credentials are highly privileged and must be protected. By using Windows Defender Remote Credential Guard to connect during Remote Desktop sessions, if the target device is compromised, your credentials are not exposed because both credential and credential derivatives are never passed over the network to the target device.
Important
For information on Remote Desktop connection scenarios involving helpdesk support, see Remote Desktop connections and helpdesk support scenarios in this article.
Comparing Windows Defender Remote Credential Guard with other Remote Desktop connection options
The following diagram helps you to understand how a standard Remote Desktop session to a server without Windows Defender Remote Credential Guard works:
The following diagram helps you to understand how Windows Defender Remote Credential Guard works, what it helps to protect against, and compares it with the Restricted Admin mode option:
As illustrated, Windows Defender Remote Credential Guard blocks NTLM (allowing only Kerberos), prevents Pass-the-Hash (PtH) attacks, and also prevents use of credentials after disconnection.
Use the following table to compare different Remote Desktop connection security options:
Microsoft Remote Desktop Save Passwords
| Feature | Remote Desktop | Windows Defender Remote Credential Guard | Restricted Admin mode |
|---|---|---|---|
| Protection benefits | Credentials on the server are not protected from Pass-the-Hash attacks. | User credentials remain on the client. An attacker can act on behalf of the user only when the session is ongoing | User logs on to the server as local administrator, so an attacker cannot act on behalf of the “domain user”. Any attack is local to the server |
| Version support | The remote computer can run any Windows operating system | Both the client and the remote computer must be running at least Windows 10, version 1607, or Windows Server 2016. | The remote computer must be running at least patched Windows 7 or patched Windows Server 2008 R2. For more information about patches (software updates) related to Restricted Admin mode, see Microsoft Security Advisory 2871997. |
| Helps prevent | N/A |
|
|
| Credentials supported from the remote desktop client device |
|
|
|
| Access | Users allowed, that is, members of Remote Desktop Users group of remote host. | Users allowed, that is, members of Remote Desktop Users of remote host. | Administrators only, that is, only members of Administrators group of remote host. |
| Network identity | Remote Desktop session connects to other resources as signed-in user. | Remote Desktop session connects to other resources as signed-in user. | Remote Desktop session connects to other resources as remote host’s identity. |
| Multi-hop | From the remote desktop, you can connect through Remote Desktop to another computer | From the remote desktop, you can connect through Remote Desktop to another computer. | Not allowed for user as the session is running as a local host account |
| Supported authentication | Any negotiable protocol. | Kerberos only. | Any negotiable protocol |
For further technical information, see Remote Desktop Protocoland How Kerberos works.
Remote Desktop connections and helpdesk support scenarios
For helpdesk support scenarios in which personnel require administrative access to provide remote assistance to computer users via Remote Desktop sessions, Microsoft recommends that Windows Defender Remote Credential Guard should not be used in that context. This is because if an RDP session is initiated to a compromised client that an attacker already controls, the attacker could use that open channel to create sessions on the user's behalf (without compromising credentials) to access any of the user’s resources for a limited time (a few hours) after the session disconnects.
Therefore, we recommend instead that you use the Restricted Admin mode option. For helpdesk support scenarios, RDP connections should only be initiated using the /RestrictedAdmin switch. This helps ensure that credentials and other user resources are not exposed to compromised remote hosts. For more information, see Mitigating Pass-the-Hash and Other Credential Theft v2.
To further harden security, we also recommend that you implement Local Administrator Password Solution (LAPS), a Group Policy client-side extension (CSE) introduced in Windows 8.1 that automates local administrator password management. LAPS mitigates the risk of lateral escalation and other cyberattacks facilitated when customers use the same administrative local account and password combination on all their computers. You can download and install LAPS here.
For further information on LAPS, see Microsoft Security Advisory 3062591.
Remote Credential Guard requirements
To use Windows Defender Remote Credential Guard, the Remote Desktop client and remote host must meet the following requirements:
The Remote Desktop client device:
Must be running at least Windows 10, version 1703 to be able to supply credentials, which is sent to the remote device. This allows users to run as different users without having to send credentials to the remote machine.
Must be running at least Windows 10, version 1607 or Windows Server 2016 to use the user’s signed-in credentials. This requires the user’s account be able to sign in to both the client device and the remote host.
Must be running the Remote Desktop Classic Windows application. The Remote Desktop Universal Windows Platform application doesn't support Windows Defender Remote Credential Guard.
Must use Kerberos authentication to connect to the remote host. If the client cannot connect to a domain controller, then RDP attempts to fall back to NTLM. Windows Defender Remote Credential Guard does not allow NTLM fallback because this would expose credentials to risk.
The Remote Desktop remote host:
- Must be running at least Windows 10, version 1607 or Windows Server 2016.
- Must allow Restricted Admin connections.
- Must allow the client’s domain user to access Remote Desktop connections.
- Must allow delegation of non-exportable credentials.
There are no hardware requirements for Windows Defender Remote Credential Guard.
Note
Remote Desktop client devices running earlier versions, at minimum Windows 10 version 1607, only support signed-in credentials, so the client device must also be joined to an Active Directory domain. Both Remote Desktop client and server must either be joined to the same domain, or the Remote Desktop server can be joined to a domain that has a trust relationship to the client device's domain.
GPO Remote host allows delegation of non-exportable credentials should be enabled for delegation of non-exportable credentials.
For Windows Defender Remote Credential Guard to be supported, the user must authenticate to the remote host using Kerberos authentication.
The remote host must be running at least Windows 10 version 1607, or Windows Server 2016.
The Remote Desktop classic Windows app is required. The Remote Desktop Universal Windows Platform app doesn't support Windows Defender Remote Credential Guard.
Enable Windows Defender Remote Credential Guard
You must enable Restricted Admin or Windows Defender Remote Credential Guard on the remote host by using the Registry.
Open Registry Editor on the remote host.
Enable Restricted Admin and Windows Defender Remote Credential Guard: Betternet 5.0.5 crack.
Go to HKEY_LOCAL_MACHINESystemCurrentControlSetControlLsa.
Add a new DWORD value named DisableRestrictedAdmin.
To turn on Restricted Admin and Windows Defender Remote Credential Guard, set the value of this registry setting to 0 to turn on Windows Defender Remote Credential Guard.
Close Registry Editor.
You can add this by running the following command from an elevated command prompt:
Using Windows Defender Remote Credential Guard
Beginning with Windows 10 version 1703, you can enable Windows Defender Remote Credential Guard on the client device either by using Group Policy or by using a parameter with the Remote Desktop Connection.
Turn on Windows Defender Remote Credential Guard by using Group Policy
From the Group Policy Management Console, go to Computer Configuration -> Administrative Templates -> System -> Credentials Delegation.
Double-click Restrict delegation of credentials to remote servers.
Under Use the following restricted mode:
If you want to require either Restricted Admin mode or Windows Defender Remote Credential Guard, choose Restrict Credential Delegation. In this configuration, Windows Defender Remote Credential Guard is preferred, but it will use Restricted Admin mode (if supported) when Windows Defender Remote Credential Guard cannot be used.
Note
Neither Windows Defender Remote Credential Guard nor Restricted Admin mode will send credentials in clear text to the Remote Desktop server.
If you want to require Windows Defender Remote Credential Guard, choose Require Remote Credential Guard. With this setting, a Remote Desktop connection will succeed only if the remote computer meets the requirements listed earlier in this topic.
If you want to require Restricted Admin mode, choose Require Restricted Admin. For information about Restricted Admin mode, see the table in Comparing Windows Defender Remote Credential Guard with other Remote Desktop connection options, earlier in this topic.
Click OK.
Close the Group Policy Management Console.
From a command prompt, run gpupdate.exe /force to ensure that the Group Policy object is applied.
Use Windows Defender Remote Credential Guard with a parameter to Remote Desktop Connection
If you don't use Group Policy in your organization, or if not all your remote hosts support Remote Credential Guard, you can add the remoteGuard parameter when you start Remote Desktop Connection to turn on Windows Defender Remote Credential Guard for that connection.
Note
The user must be authorized to connect to the remote server using Remote Desktop Protocol, for example by being a member of the Remote Desktop Users local group on the remote computer.
Considerations when using Windows Defender Remote Credential Guard
Windows Defender Remote Credential Guard does not support compound authentication. For example, if you’re trying to access a file server from a remote host that requires a device claim, access will be denied.
Windows Defender Remote Credential Guard can be used only when connecting to a device that is joined to a Windows Server Active Directory domain, including AD domain-joined servers that run as Azure virtual machines (VMs). Windows Defender Remote Credential Guard cannot be used when connecting to remote devices joined to Azure Active Directory.
Remote Desktop Credential Guard only works with the RDP protocol.
No credentials are sent to the target device, but the target device still acquires Kerberos Service Tickets on its own.
The server and client must authenticate using Kerberos.
Posted on Friday, January 27, 2017 by Sam
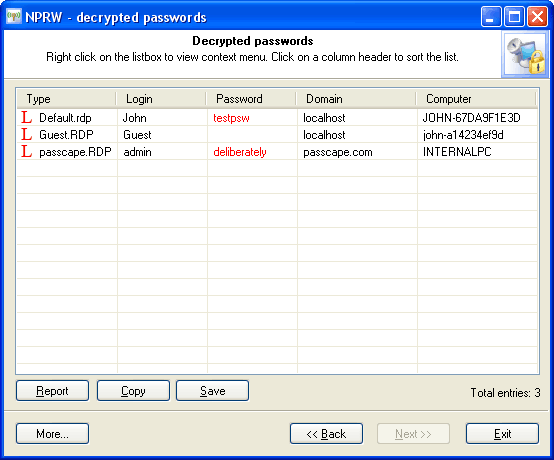
I often use Remote Desktop Connection Manager (RDCMan) to connect to various servers at work and at home. It has a very handy feature of saving the login credentials either per server or better; per server grouping. The password is stored in the .rdg file that is saved out by the application in an encrypted format so that the password can't be easily read.
After enough time goes by I tend to forget what the password is and inevitably I will run into a situation where I want to find out what it is. For example maybe I want to connect via remote desktop on another computer and want to set up the remote server configurations again in a remote desktop app other than RDCMan.
Opening the .rdg file shows that it's stored in XML format. Look for a <password> element e.g.
Take note and/or copy the encrpyted string value. We will use this in the next step.
Microsoft Remote Desktop Save Password Group Policy
Decryption
RDCMan.exe contains a DecryptString method which isn't exposed in the application but can be called externally if the application is referenced as a library from another application.
If you have RDCMan installed on your Windows system it should be located here:
Microsoft Remote Desktop Save Password
- Copy the .exe file to another location (perhaps on your Desktop) and rename the file to be 'RDCMan.dll'
- Open up Visual Studio (using 2015 at the time of this writing) and create a new Unit Test or Console app project.
- Copy the DLL file into your project and add a reference to it.
- Then either in your console app's main method or in a unit test class copy in this code:
- Build your project and run it and you should be able to get your clear password back out.
Microsoft Remote Desktop Save Password Manager
Example Unit Test project is available here https://github.com/swinter2/RDCManTest